Webex Ranks Best of Breed in NSA Collaboration Services Guidelines

Guidelines for a Safe, Secure, and Compliant Collaboration Ecosystem
The National Security Agency (NSA) published a set of guidelines for “Selecting and Safely Using Collaboration Services for Telework.” The guidelines that evaluated 17 collaboration service providers identified a dozen critical criteria for cybersecurity functionality and security assurance to help government employees and organizations make informed decisions when selecting a collaboration service for their needs. The goal is to help users “draw down their risk exposure” when conducting business throughout their workday.

The pandemic brought about a new hybrid nature of how we work. This sea change has raised new compliance issues that did not necessarily exist in the past when work happened in an organization’s building and on secure, internal networks using the organization’s devices. Today, IT Admins need to worry about data protection and compliance while expanding the technology footprint by including off-premises and personal devices.
In an article also published today, my colleague Radhi Chagarlamudi discusses how the NSA’s guidelines shine a spotlight on why organizations need to consider security across the entire collaboration ecosystem. She rightly calls out why leaders need to consider the collaboration services users employ throughout their day, whether each service is secure, and how IT Admins can manage the ecosystem and address issues as they come up.
Breadth and Depth for Security in Collaboration Services
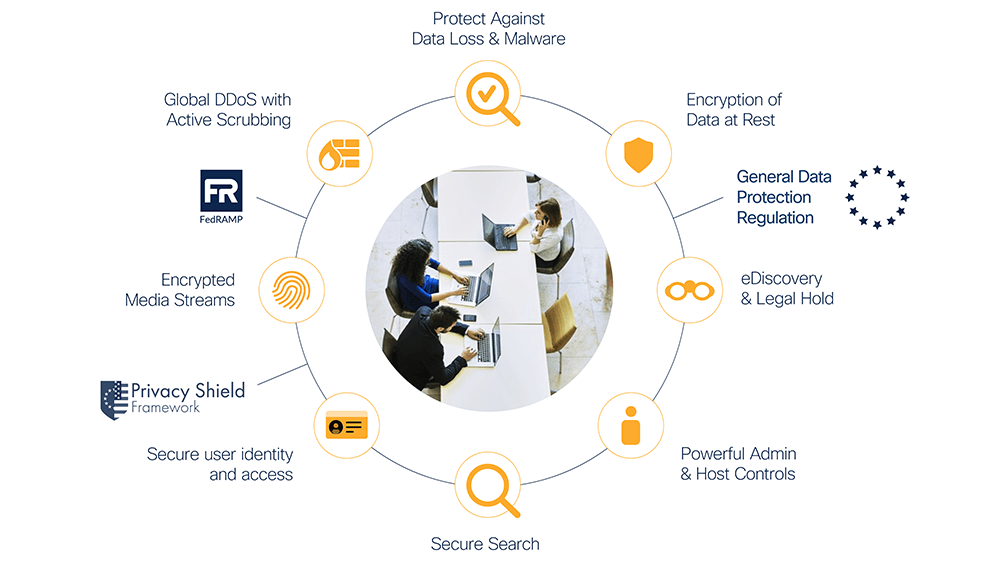
Whether in the office, at home, or on the go, our approach to securing devices, content, applications, data, and users is holistic and 360-degree in nature. We help to authenticate those users by easily integrating with existing identity providers already used in many organization’s environments for consistent application of their policies.
For many years, customers have entrusted Cisco Webex with their mission-critical collaboration, meetings, messages, calling, and data. They look to Webex to protect their data, help them abide by privacy laws and regulations, and reduce the risk of exposure to competitors, proprietary or sensitive data becoming public, unwanted press, and a bad reputation. Webex provides a hardened collaboration platform that helps keep customers’ data secure by making privacy and security the top priority in the design, development, deployment, and maintenance of our networks, platforms, and applications. Webex employs multiple technologies, procedures, and teams to ensure the collaboration platform meets privacy and security requirements and gives customers a choice of region to store their user content.
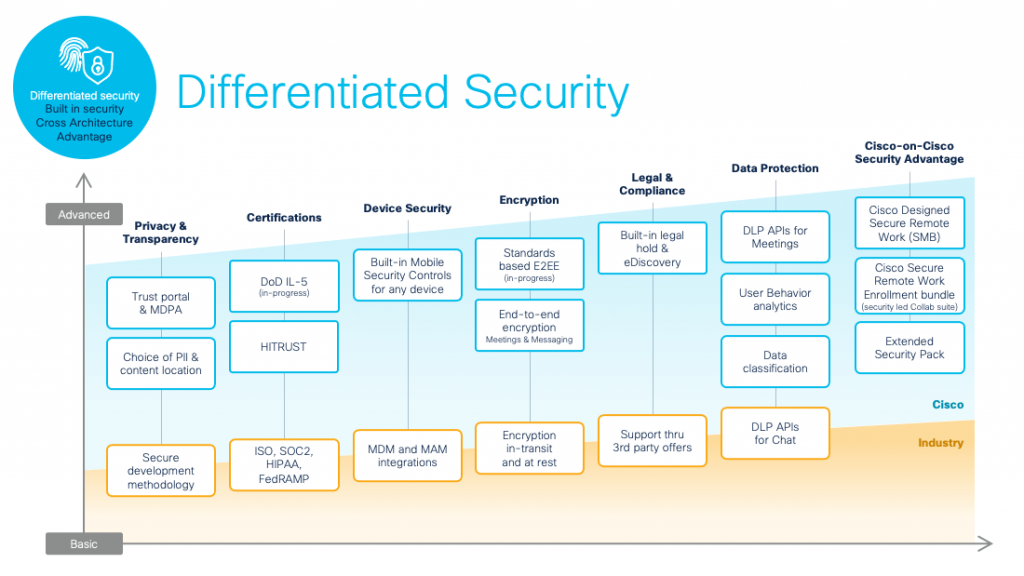
Webex has a repeatable and measurable process in its Secure Development Lifecycle. This includes threat modeling, secure design and coding, vulnerability testing, privacy impact assessments, and third-party security assessments. We assess and remediate vulnerabilities on an ongoing basis and monitor networks and systems to detect outages, service latency, and unusual and unauthorized activities and events. We also have a privacy program based on “privacy by design” to protect our customers’ Personally Identifiable Information (PII). The program includes a Privacy Impact Assessment (PIA), incident response, notice to customers, and management of subject requests.
Secure Across the Ecosystem
The Cisco Webex ecosystem addresses core security criteria like multi-factor authentication and controlling how collaboration invitations are shared. But we go beyond that. At Webex, where security is “built-in and not bolted on,” we provide true end-to-end encryption for text messages, meetings, file sharing, and screen sharing – all criteria noted by the NSA in its report. While the Webex App provides a rich user experience for users, our systems ensure that the user and organization’s data is secure across the board. Let me highlight a few examples of how we go beyond in our mission of security and compliance.
Securing Users and Devices
To further secure user access, Webex has automated user on-boarding and off-boarding (SCIM or AD Sync), single sign-on with customer’s choice of identity provider, multi-factor authentication via Cisco Duo or HOTP Authenticator, standard OAuth 2.0-based authorization, anonymized user identities, role-based feature access control, and delegated administration.
When using Webex, we also secure the user’s devices. All content created in Webex is encrypted end-to-end — even the cached content. Our built-in MDM capabilities thru Webex Control Hub ensure secure access for devices, including PIN lock to launch the app, admin controls for file sharing, and the disabling of message notification previews so no one can snoop messages on a locked screen and ability to remotely wipe Webex messages in case of loss of device or theft.
Securing Content and Meetings
End-to-end encryption keeps all Webex content secure, including searches. Organizations also have the option to store their encryption keys on-premises, providing them ultimate control. With the end-to-end encrypted option for meetings, customers have exclusive control of the meeting encryption keys, and Cisco and anyone cannot access their meeting content. We have been doing this for 12+ years and just announced a new standards-based approach to Meetings end-to-end encryption that also provides end-to-end verified identity and support for conference room devices.
Data Loss Protection (DLP)
At Webex, we’ve designed our ecosystem to help to keep users from making mistakes before they happen. Through our Data Loss Prevention (DLP) features, organizations can prevent important information from being shared maliciously or accidentally in meetings or messaging. Organizations can track meeting content, messages, and files that are posted in spaces, track users added to spaces and meeting attendees, control unwanted users in spaces, and avoid accidental or deliberate sharing of sensitive data and information. Webex is the only collaboration solution that enables customers to use their existing DLP tools and policies for meetings recordings and transcripts.
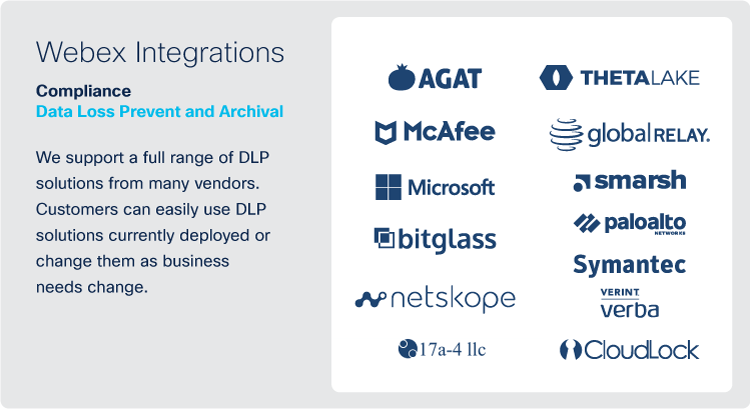
Built-in Compliance
With Webex Control Hub, organizations can define their data retention policy for meetings and messaging, including transcripts, highlights, recordings, and messaging content. Organizations can easily search meetings and messaging content using the eDiscovery search and extraction tool. This solution provides support for any required cloud security compliance certifications and compliance regulations. In addition, IT Admins are provided with controls to minimize their risk profile including disabling sharing of files for high-risk users, disabling screen sharing, or controlling external and internal communications.
Extending Security Capabilities: Cisco-on-Cisco Security Advantage
To extend the security capabilities of Webex, best-of-breed integrated solutions can be quickly deployed to protect an organization’s data as well as the data of its partners. They prevent sensitive data leakage and provide anti-malware protection and multi-factor authentication.
To ensure users adhere to compliance policies, Cisco Cloudlock provides visibility into and control over sensitive information stored in Webex messaging with more than 80 existing policies and an ability to create new policies. Cloudlock can automatically delete files or messages when policy violations are discovered, notify admins, and remove users from spaces.
To help fight malware attacks, Cisco TalosClamAV scans all files uploaded for Trojan attacks, viruses, malware, and other malicious threats. All files shared in Webex that an organization designates are scanned and remediated, even if uploaded by external users. Infected files will be marked clearly, and end-users will not be able to download them on both organization-managed and personally managed devices. Cisco TalosClamAV scans one billion files daily for over 10 million users, with 7.2 trillion attacks stopped every year.
Security for the Remote Worker
Securing the remote user and their data will continue to be a prime directive in the new hybrid work model. Whether users are working from home, in shared co-working offices, or remote offices, the same security coverage inherent with on-premises work needs to be extended to these workers in the hybrid model. To further enhance security for the remote worker, Webex has created a cost-effective suite of solutions for enterprise and SMB organizations alike. With Cisco Webex Secure Remote Work solutions, services such as meetings, messaging, and calling are secure. But that security coverage extends to endpoints, multifactor authentication, DNS protection, and malware defense for inbound and email.
____________________________________________________________________________________
*Related to the Blog post above.
Current Technologies CLC also has the following Custom Collaboration / WebEx courses, click the link below.
Check out our Custom Collaboration Courses
If you have any questions let us know.
Current Technologies Computer Learning Center
6210 Central Avenue
Portage, Indiana 46368
Phone: 219-764-3800
Fax: 219-764-3805
Email: info@ctclc.com
.png)






